I’m documenting terms I’ve encountered or learned while communicating and working in the workplace, so I won’t forget them and can refer back to them occasionally. This collection covers terminology used not only in software engineering but across business in general.
Table of Contents
- MECE
- Dogfooding
- ISO 8601
- Ice Breaking
- Housekeeping Job
- On-the-fly
- SLA/SLO/SLI
- Dogpile Effect
- Thundering Herd
- Zero Trust
- Shift Left
- Technical Debt
MECE
 Source: Logical Analysis MECE without Duplication and Omission
Source: Logical Analysis MECE without Duplication and Omission
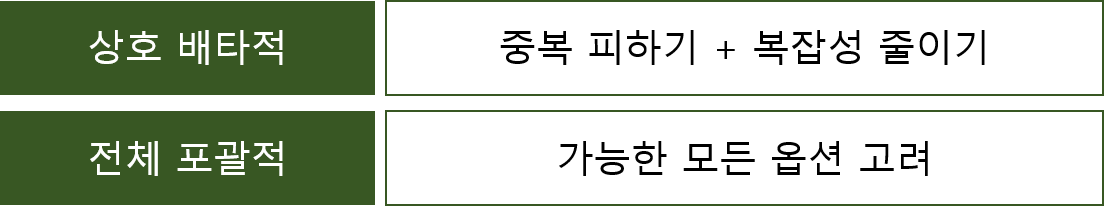
Mutually Exclusive Collectively Exhaustive is an acronym meaning dividing solutions to a problem so they don’t overlap while covering everything completely. In other words, without duplication and omission.
Definition
- Mutually Exclusive: Items should not overlap with each other
- Collectively Exhaustive: All possibilities should be included without exception
Application in Software Engineering
While this term is known as a business management concept, it’s equally applicable to software engineering. This is because eliminating duplicate code while keeping things simple but including all necessary functionality is a common principle in software design and development.
Practical Application Examples:
Error Code Classification in API Design
- 4xx: Client errors (400, 401, 403, 404…)
- 5xx: Server errors (500, 502, 503…)
- Each category doesn’t overlap while covering all error cases
Writing Test Cases
- Normal cases (Happy Path)
- Boundary cases (Edge Cases)
- Exception cases (Error Cases)
Microservice Domain Separation
- User Service
- Order Service
- Payment Service
- Each service is independent while covering the entire business
When selecting action items to resolve issues or conceptualizing software features, intentionally using this concept often leads to good designs and solutions.
References
Dogfooding
In 1988, Paul Maritz, a manager at Microsoft, sent an internal email titled “Eating our own Dogfood” to test manager Brian Valentine, urging employees to use more of their own products, which made the term famous. (Wiki Article)
Definition
Translated literally as eating dog food, this is a slang term meaning the act of software creators using their own products.
Importance in Software Development
When using your own software according to user scenarios, improvement points become visible:
- ‘This could be handled better this way!’
- ‘I didn’t consider this part, need to improve it!’
- ‘This error message would be hard for users to understand’
Real-World Examples
| Company | Product | Dogfooding Method |
|---|---|---|
| Microsoft | Windows | Using internal builds first |
| Gmail, Docs | Deploying internally first | |
| Slack | Slack | Using as internal communication tool |
| Airbnb | Airbnb | Employees booking accommodations themselves |
No matter how much thought goes into software design and development, things are often missed. Based on this experience, the process of developers directly using and improving products with the mindset of providing a more complete product to users is important.
ISO 8601
ISO 8601 is an international standard for date and time representations.
Standard Format
Importance in Software Development
Handling data that follows standards has the following benefits:
- Reduced Parsing Complexity: No need for code to handle various date formats
- Internationalization Support: Clear timezone handling
- Easy Sorting: Chronological sorting possible with string sorting
- Debugging Convenience: Easy to identify times in logs
Practical Application Examples
| |
When handling data, try to follow standards whenever possible.
Ice Breaking
The process of using comfortable topics to ease a stiff and tense atmosphere before moving on to serious discussions.
Purpose
- Reducing psychological barriers between participants
- Creating an environment for free communication
- Encouraging creative idea generation
- Team building and trust formation
Usage in Practice
Official discussions and work often create stiff and formal relationships, but using ice breaking techniques effectively can be beneficial.
Simple Ice Breaking Techniques:
- Two Truths and a Lie: Participants tell two truths and one lie, others guess
- Check-in Question: “If you described today’s mood as weather?”
- Quick Poll: “Morning person vs Night owl”
- Photo Share: “Share one recent photo”
Housekeeping Job
A term used to describe tasks performed periodically on servers for minor maintenance (log rotation, etc.).
Representative Housekeeping Tasks
| Task | Description | Frequency |
|---|---|---|
| Log Rotation | Compress/delete old log files | Daily/Weekly |
| Temp File Cleanup | Clean up temporary files | Hourly |
| Session Cleanup | Clean up expired sessions | Per minute |
| Database Vacuum | DB optimization | Weekly/Monthly |
| Cache Invalidation | Remove old cache | Hourly |
| Backup Rotation | Delete old backups | Weekly |
Implementation Example (Cron)
| |
On-the-fly
Meaning “on the spot” or “as it happens,” used occasionally.
Meaning in Software
- Real-time Processing: Processing immediately when a request comes in
- Dynamic Generation: Creating things when needed rather than in advance
- Streaming: Processing in real-time without downloading everything
Actual Usage Examples
In Collaboration:
- “If issues arise, I’ll support you on-the-fly”
- Meaning providing support immediately when requests come in
Technical Usage:
On-the-fly transcoding: Real-time video format conversion on serverOn-the-fly compression: Immediate compression during transmissionOn-the-fly encryption: Immediate encryption during storage
Pros and Cons
| Advantages | Disadvantages |
|---|---|
| Saves storage space | Possible processing delay |
| Always latest data | Increased CPU usage |
| Flexible response | Unpredictable performance |
SLA/SLO/SLI
Metrics for measuring and managing service reliability.
Definitions
| Term | Full Name | Description |
|---|---|---|
| SLA | Service Level Agreement | Service level contract |
| SLO | Service Level Objective | Service level objective |
| SLI | Service Level Indicator | Service level indicator |
Relationship
Practical Examples
Availability:
- SLI: Actual uptime / Total time × 100
- SLO: 99.9% availability target
- SLA: Service credit if below 99.9%
Latency:
- SLI: P95 response time
- SLO: P95 response time under 200ms
- SLA: Compensation if exceeding 500ms
Dogpile Effect
A phenomenon where multiple requests simultaneously try to fetch original data when cache expires.
Problem Scenario
Solutions
1. Using Mutex/Lock:
| |
2. Cache Warming:
| |
Thundering Herd
A phenomenon where a large number of requests occur simultaneously due to specific events (server restart, network recovery, etc.).
Occurrence Scenario
- DB server restarts
- Thousands of pending connection attempts
- All try to connect simultaneously → DB overload
- Connection failure → Retry → Vicious cycle
Solutions
1. Exponential Backoff:
| |
2. Adding Jitter:
| |
Zero Trust
A security principle of “never trust, always verify.”
Core Principles
- Never Trust, Always Verify: Verify all access
- Least Privilege: Grant minimum permissions
- Assume Breach: Design assuming compromise
Traditional Model vs Zero Trust
| Aspect | Traditional Model | Zero Trust |
|---|---|---|
| Trust Boundary | Network perimeter | None |
| Authentication | Once (at login) | Continuous |
| Permissions | Broad | Minimal |
| Monitoring | Selective | All activity |
Shift Left
An approach of performing quality control activities in the early stages of the development lifecycle.
Traditional vs Shift Left
Application Areas
| Area | Shift Left Activities |
|---|---|
| Testing | TDD, Unit tests |
| Security | SAST, Code reviews |
| Performance | Early load testing |
| Operations | IaC, DevOps |
Benefits
- Early bug detection → Reduced fix costs
- Faster deployment
- Improved quality
- Enhanced developer capabilities
Technical Debt
Choices that are efficient in the short term for fast development but incur additional costs in the long run.
Types
- Intentional Debt: Consciously sacrificing quality to meet deadlines
- Unintentional Debt: Occurring due to lack of experience or knowledge
- Bit Rot: Debt from software aging
Management Methods
Debt vs Investment
| Situation | Choice | Reason |
|---|---|---|
| MVP Development | Accept debt | Quick market validation |
| Core Features | Minimize debt | Long-term maintenance |
| POC | Debt irrelevant | Planned for disposal |
To be continued…
I plan to continuously update this document whenever I discover new terminology. As a software engineer, understanding terms used in both business and technology is key to effective communication.